Security Response Efficiency Increased Tenfold: QAX Released Third Generation SOAR
Date:Dec 24,2020 Author:QAX
"Security and operations work separately, security capabilities are not fully integrated, massive alerts are tired of responding, communication depends on roaring operations, and system processes are idling...", the director of the information security center of a large central enterprise said that there are five major pain points in current security operations: people less than things, alert fatigue, slow response, knowledge lost, lack of collaboration. Security operations urgently needs to be upgraded.
On December 24, QAX officially released the third generation of security orchestration, automation and response product (SOAR 3.0) in Beijing. This product is based on automated and intelligent cybersecurity detection and response capabilities to help enterprises and organizations create a practical operations system, the efficiency of security reponse is increased by more than tenfold.
QAX Group President Yunkun Wu said that SOAR is not only a product, but also a platform, representing an emerging field that deeply integrates security, IT and people. By using systematic methods, SOAR is about to achieve routine operations and actual combat attack and defense, and provide solid support for users to achieve the "three lizations and six defenses".

Security Operations Embrace the SOAR Era
In the past months, the industry has exposed two large-scale cyberattacks one after another: including the FireEye weapon arsenal leak and the SolarWinds supply chain attack. It is obvious that the cybersecurity posture is getting more and more serious. By looking at the experience of in the past few years, enterprises and organizations still seem to be incapable of responding organized and systematic cyberattacks.
Most organizations have not established an effective security operations system. From the detection of threats to the response of threats, it takes too much labor and time costs.
Especially in the response progress. On the one hand, threat handling requires coordination and linkage between different security devices, which is time-consuming and laborious to rely on manual operations; on the other hand, there is a shortage of responders, and the skill level is difficult to improve due to repetitive labor, and the experience of excellent engineers is also difficult to form standardized processes and actions.
"SOAR is not just a product or a tool." said Yunkun Wu, the President of QAX Group. "From the simple system module in SOAR 1.0 to the automated response tool in SOAR 2.0 to today's SOAR, it represents the development trend of security operations."
Wu emphasized that from the end of the "Chinese 13th Five-Year Plan" to the beginning of the "14th Five-Year Plan", this has pushed cybersecurity into another "first year". SOAR is the key to the implementation of the organization.
Gartner data shows that as a relatively new technology, SOAR has received extensive attention from the market since its birth. It is estimated that by 2023, the SOAR market revenue will reach 550 million U.S. dollars.
Time for Security Response is Reduced to Minutes
SOAR greatly improves the response efficiency. In practice, QAX found that in the scenario of one-click blocking of IP in emergency, manual handling of a small number of alerts takes 20 minutes or more, while using SOAR it only takes 10 seconds, and less than 3 minutes total including manual confirmation. If there are tens of thousands of alerts under the conditions, it is more difficult to handle manually, but SOAR can be handled in full, and the duration is only on the minute level.
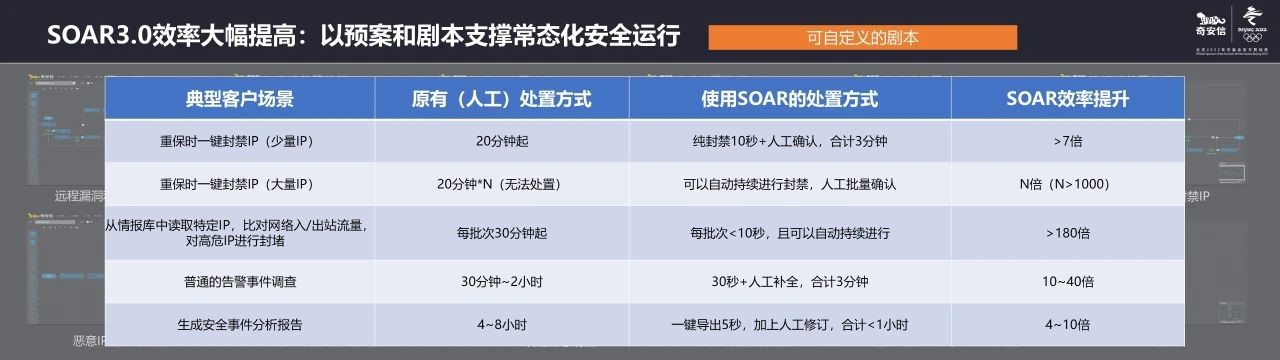
In the link of threat intelligence matching and high-risk IP blocking, manual processing can only process part of the IP every day, and each processing takes more than half an hour; relying on SOAR to identify and block each IP only takes less than 10 seconds, and can continue to do it, and the efficiency is greatly improved.
In the process of generating a security incident report, it takes 4 to 8 hours for manual writing, and only a few seconds for SOAR to do one-click export. With manual revision, the total time can be controlled within 1 hour.
Overall, SOAR can increase the efficiency of security incident investigation and response operations by more than 10 times; for operations that require repetitive and continuous operations, the improved efficiency is hundreds of times. Because of this, SOAR has been welcomed by large enterprises and organizations.
Six Major Features makes Routinized Operations of Cybersecurity into Reality
QAXN SOAR 3.0 takes actual combat as the core, to help companies and organizations to sort out the complicated security operations process into tasks and playbooks, transform decentralized security tools and functions into programmable applications and actions, and to use orchestration and automation technology to cooperate with teams, tools, and processes, so that it would cover all aspects of security operations, such as protection, detection, and response.
QAX SOAR products have the following key features:
First of all, security capability orchestration can standardize the scattered security capabilities and response processes of customers, form a playbook library and application library that can be called at any time, realize the integration and coordination of teams, tools, and processes, and reduce manual intervention.
Secondly, security process automation can automate security capabilities through functions such as automated alerts handling, automated playbook execution, and automated service invocation.
Thirdly, the intelligent alert response can intelligently triage massive amounts of alert information, thereby automatically triggering a well-arranged process, just like a hospital triage table. On the one hand, alerts triage can automatically aggregate alerts information and calculate the credibility and priority of the alert; on the other hand, it can conduct supplementary investigation and analysis of the alert information, which is convenient for engineers to conduct further research and judgment.
At the same time, case management can help users conduct process-based and continuous investigation, analysis, and response handling of a set of related alerts, and continuously accumulate artifacts and attackers' attack tactics.
Finally, QAX SOAR has an open system architecture, it adopts open programmable architecture design, built-in workflow engine and application development kit; users can customize playbooks, applications, automatic response trigger conditions and case handling procedures, and seamlessly integrate into existing security system.
On the basis of the above five core capabilities, the new version of QAX SOAR has added the collaborative war room function, which not only realizes real-time communication between security engineers, but also has built-in a large number of well-organized automated playbooks and actions to realize the interaction between people and machine. Cooperative processing has changed the situation that "communication basically relies on roaring, and operations basically relies on hands", and further improves the efficiency of coordinated operations.
The QAX SOAR product director vividly compares SOAR to a master symphony conductor, allowing the orchestra composed of various security products to perform their respective strengths and collaborate to perform beautiful movements.
Gartner survey found that with the development of security technology, many tools already have SOAR or integrated SOAR modules, such as SIEM and other devices already include workflow automation and other related functions.
As a leading company in domestic cybersecurity industry, the new version of SOAR released by QAXN this time can be deployed independently or in conjunction with SOC and other solutions. It has more advantages in functions and performance, and can truly integrate security teams, tools and processes.
At the same time, during the period of cybersecurity guarantee for major events, QAX SOAR can also help customers formulate plans in advance to wait for work, respond automatically and quickly deal with them during the event, summarize and accumulate experience after the event, and improve the practical, systematic, and routinized security operation in an all-round level.